Xinan Yan, PhD candidate
David R. Cheriton School of Computer Science
Abel Molina, PhD candidate
David R. Cheriton School of Computer Science
Yao (1993) proved that quantum Turing machines and uniformly generated quantum circuits are polynomially equivalent computational models: t >= n steps of a quantum Turing machine running on an input of length n can be simulated by a uniformly generated family of quantum circuits with size quadratic in t, and a polynomial-time uniformly generated family of quantum circuits can be simulated by a quantum Turing machine running in polynomial time.
Hemant Saxena, PhD candidate
David R. Cheriton School of Computer Science
We address the problem of discovering dependencies from distributed big data. Existing (non-distributed) algorithms focus on minimizing computation by pruning the search space of possible dependencies. However, distributed algorithms must also optimize data communication costs, especially in current shared-nothing settings.
Professor Brian Forrest
Department of Pure Mathematics, University of Waterloo
There are many challenges to teaching mathematics in a fully online environment. In this talk I will show the important role that assigned work plays in mitigating many of these challenges. I will also speak about how my experience in teaching online has impacted the way in which I approach my on campus courses.
Jeff Avery, PhD candidate
David R. Cheriton School of Computer Science
Amine Mhedhbi, PhD candidate
David R. Cheriton School of Computer Science
We study the problem of optimizing subgraph queries (SQs) using the new worst-case optimal (WCO) join plans in Selinger-style cost-based optimizers. WCO plans evaluate SQs by matching one query vertex at a time using multiway intersections. The core problem in optimizing WCO plans is to pick an ordering of the query vertices to match.
We make two contributions:
Nate Cardozo, Senior Staff Attorney
Electronic Frontier Foundation
Encryption is legal in the Five Eyes countries, thanks to our victory in what’s come to be known as the Crypto Wars of the 1990s. Computer security research is increasingly viewed as a boon rather than a scourge. But time is a circle and once again, law enforcement and policy makers around the world are calling for all that to change.
Bushra Aloraini, PhD candidate
David R. Cheriton School of Computer Science
Yuwei Jiao, Master’s candidate
David R. Cheriton School of Computer Science
Andrew Beltaos / Amenda Chow
University of Waterloo / York University
Teaching via analogies builds upon students' existing knowledge. New concepts that are taught only within the context of mathematics may seem foreign to students at first glance, but if students have already learned analogous concepts elsewhere in life, as educators, we can make use of their existing framework to strengthen their learning.
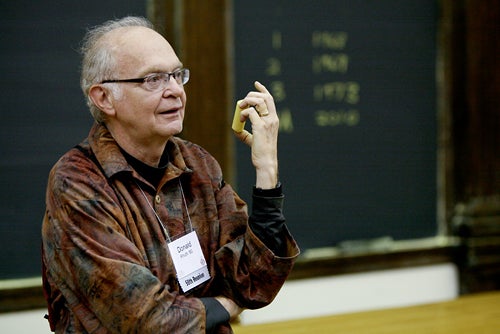
Donald E. Knuth
Professor Emeritus of The Art of Computer Programming
Stanford University
Abstract: The speaker will answer any question on any subject.
Mustafa Korkmaz, PhD candidate
David R. Cheriton School of Computer Science
Data centers consume significant amounts of energy and consumption is growing each year. Alongside efforts in the hardware domain, there are some mechanisms in the software domain to reduce energy consumption. One of these mechanisms is dynamic voltage and frequency scaling (DVFS) and modern servers which are equipped with multi-core CPUs.
Vijay Ganesh, ECE
University of Waterloo
Aaron Moss, PhD candidate
David R. Cheriton School of Computer Science
Rafi Shan Turas, Master’s candidate
David R. Cheriton School of Computer Science
Ingrid Daubechies
James B. Duke Professor of Mathematics and Electrical and Computer Engineering, Duke University
2018 University of Waterloo Doctor of Mathematics, honoris causa
This inaugural Distinguished Lecture in Applied Math will be given in DC 1302, with a reception to follow in DC 1301, the Fishbowl.
Antonina Kolokolova, Department of Computer Science
Memorial University of Newfoundland
A unifying theme in complexity theory in the past few years has been the duality between lower bounds and algorithms. Indeed, some of the main recent lower bounds have been proven by developing better algorithms.
Mina Farid, PhD candidate
David R. Cheriton School of Computer Science
RDF has become a prevalent format to represent disparate data that is ingested from heterogeneous sources. However, data often contains errors due to extraction, transformation, and integration problems, leading to missing or contradicting information that propagate to downstream applications.
Ben Armstrong, Master’s candidate
David R. Cheriton School of Computer Science
Carolyn Lamb, PhD candidate
David R. Cheriton School of Computer Science
This thesis is driven by the question of how computers can generate poetry, and how that poetry can be evaluated. We survey existing work on computer-generated poetry and interdisciplinary work on how to evaluate this type of computer-generated creative product.
Anonymization with Differential Privacy • Ben Weggenmann
SAP Security Research
Cristina Tavares, Master’s candidate
David R. Cheriton School of Computer Science
Amira Ghenai, PhD candidate
David R. Cheriton School of Computer Science
Ju Wang, Postdoctoral fellow
David R. Cheriton School of Computer Science
Passive radio frequency identification (RFID) tags are ubiquitous today due to their low cost (a few cents), relatively long communication range (7–11 m), ease of deployment, lack of battery, and small form factor. This talk shows how even hobbyists can transform commodity RFID tags into sensors by physically altering ('hacking') them using COTS sensors and a pair of scissors. Importantly, this requires no change to commercial RFID readers.
Chathura Kankanamge, Master’s candidate
David R. Cheriton School of Computer Science





