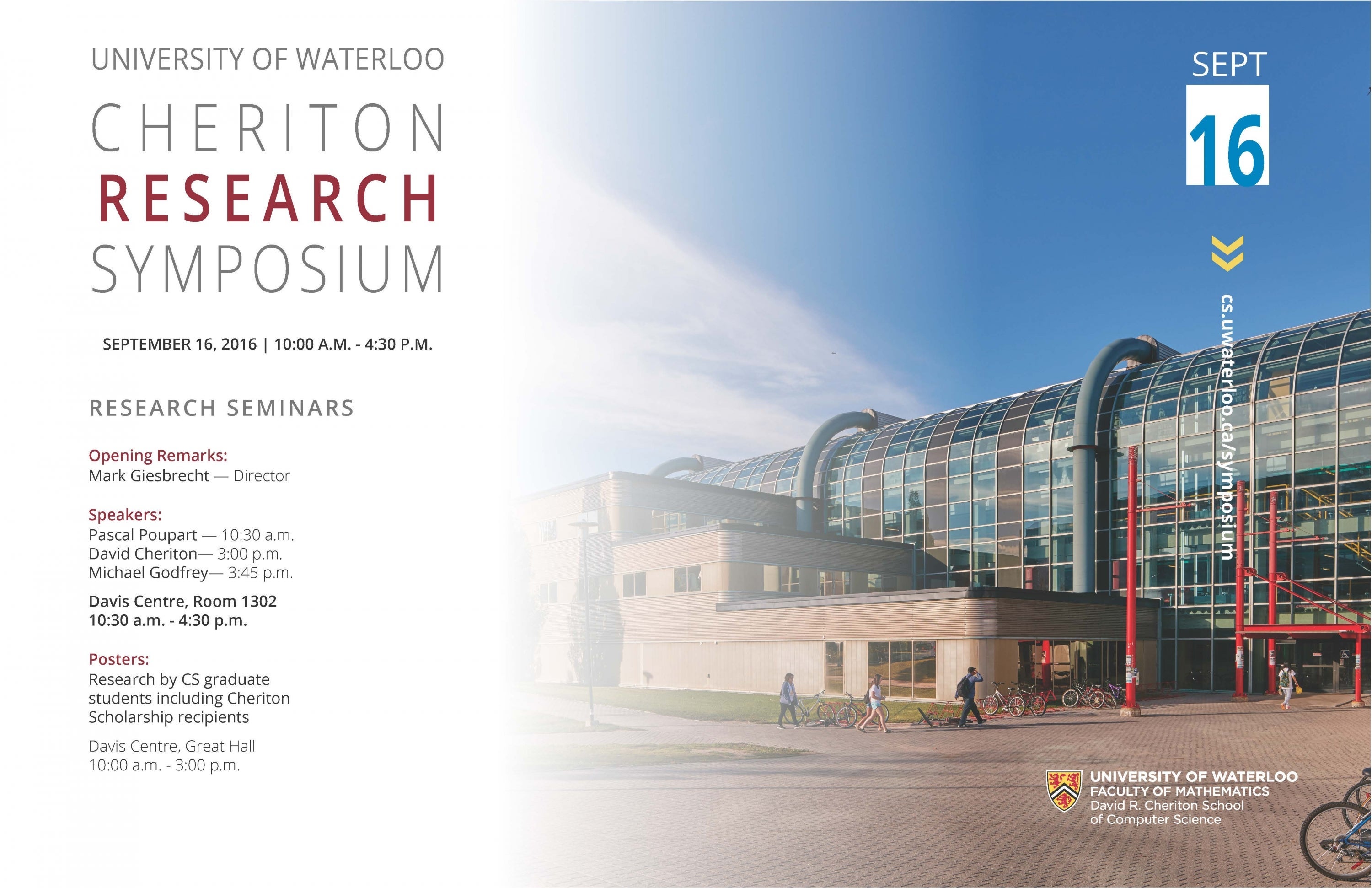
The Cheriton School of Computer Science will hold its annual Cheriton Research Symposium September 16 in the Davis Centre.
This year's symposium will consist of talks by Pascal Poupart, David Cheriton, and Michael Godfrey
Posters by graduate students including Cheriton Graduate Student Scholarship recipients will be on display in the Great Hall, Davis Centre from 10:00 am to 3:00 pm.
Schedule of the day
| Time | Description |
|---|---|
|
10 a.m. - 3 p.m. | DC Great Hall - Poster Session |
| 10:30 a.m. |
DC 1302 - Mark Giesbrecht — Welcome and Opening Remarks |
|
10:30
a.m.
- |
DC
1302
-
Pascal
Poupart
— Leveraging
Data
Science
to
Directly
Learn
Tractable
Models
for
Probabilistic
Inference
and
Decision
Making |
|
12
p.m.
- | DC 1301 - Lunch |
| 3 p.m. - 3:45 p.m. |
DC 1302 - David Cheriton - Teaching Computational (Systems) Thinking and Computer Systems in the Real World |
| 3:45 p.m. - 4:30 p.m. |
DC 1302 - Michael Godfrey - Does your mother know you're here? Understanding software artifact provenance "Provenance" is a term from archaeology and the arts that refers to a set of evidence supporting the claimed origin of an artifact, such as a piece of pottery or an oil painting. Recently, the term has been used in an electronic context --- "digital provenance" --- to indicate an artifact such as a software component or set of data, really is what it claims to be and should be permitted to be used within sensitive operating environments.
In
this
talk,
I
suggest
how
we
can
stretch
the
definition
further
to
encompass
"software
artifact
provenance". That
is,
for
a
given
software
development
artifact
such
as
a
feature,
a
source
code
snippet,
or
a
third-party
library,
we
might
want
to
ask
the
question:
Where
did
this
come
from
and
what
is
the
evidence? For
example,
one
might
wonder
how
a
given
feature
was
decided
upon
during
a
mailing
list
discussion,
how
it
manifested
itself
in
the
code,
and
how
it
has
been
maintained
since
the
initial
implementation.
For
a
given
code
snippet,
one
might
wonder
about
its
history
within
the
design
of
the
system:
Was
it
designed
to
fit
exactly
here,
or
was
it
moved
or
copied
from
elsewhere?
And
for
a
given
third-party
jar
file
that
has
been
included
in
a
Java
system
distribution,
one
might
ask:
What
version
of
the
library
is
this,
and
how
do
we
know?
In
this
talk
I
will
sketch
some
of
the
ideas
behind
this
work,
and
show
how
we
might
phrase
some
of
these
questions
in
terms
of
concrete
criteria.
In
particular,
we
will
concentrate
on
simple
techniques
for
reducing
a
large
search
space
of
candidates
down
to
a
small
handful
that
can
be
examined
in
detail
using
more
expensive
techniques.
A
concrete
example
of
investigating
third-party
libraries
in
Java
systems
will
be
presented.
|
Poster session winner will be announced after the last talk of the day.
Previous symposiums