We’ve connected billions of devices to the Internet and in the coming years we’ll connect billions more. Many of these Internet of things or IoT devices have sensors in them to detect their environment — from a room’s ambient temperature and light levels to sound and motion.

Dr. Ju Wang (centre) and Professor Omid Abari demonstrate the wireless keypad clicker they invented by hacking RFID sensors with tiny push-button switches.
One of the biggest challenges is making these devices sustainable and battery free. If an IoT device can operate without a battery it lowers maintenance costs and allows the device to be placed in out-of-reach areas.
Professor Omid Abari, Postdoctoral fellow Ju Wang and Professor Srinivasan Keshav have taken a large step towards that goal. By hacking radio frequency identification tags — those ubiquitous squiggly ribbons of metal with a tiny chip found in all manner of objects — they have given these inexpensive devices the ability to sense the environment.
“It’s really easy to do,” Wang said. “First, you remove the plastic cover from the RFID tag, then cut out a small section of the tag’s antenna with scissors, then attach a sensor across the cut bits of the antenna to complete the circuit.”
An RFID tag is an identification system that uses a small radio frequency device to identify and track objects. An RFID tagging system includes the tag itself, which consists of a small antenna, chip and memory; an external device sometimes called a reader or transponder that sends wireless signals to and from the tag and provides the energy that operates the chip; and an application that collects and processes data from the reader.
RFID tags are commonly used to track inventory in warehouses and factories, to prevent theft of merchandise in stores, in libraries to keep track books and DVDs, and in debit cards to make contactless payment possible — they’re even found in guitars, casino chips, and dogs and cats that have been microchipped.
But in their stock form RFID tags provide only identification and location. It’s the hack Abari’s team has done — cutting the tag’s antenna and placing a sensing device across it — that gives the tag the ability to sense its environment.
To give a tag eyes, the research team hacked an RFID tag with a phototransistor, a tiny sensor that responds to different levels of light. “By exposing the phototransistor to light it changes the characteristics of the RFID’s antenna, which in turn causes a change in the signal going to the reader,” Abari explained. “We developed an algorithm on the reader side that monitors change in the tag’s signal, which is how it senses light levels.”
But that’s just the first step towards a light-sensing application. If several tags are similarly hacked and placed in a row or grid, the devices can be used to detect motion. “We placed several RFID tags modified with light sensors on a surface,” Wang explains. “The shadow cast by your hand as you sweep it across the bank of tags can be used to detect movement or to respond to hand gestures.”
Similar hacks give RFID tags the ability to detect temperature. “A thermistor is a temperature-sensitive resistor, so as ambient temperature changes so does the resistance of the device, which in turn changes the characteristics of the RFID’s antenna. The reader detects this change and with the algorithm we developed we can infer temperature,” Abari said.
Among the simplest of hacks is adding a switch to an RFID tag so it can act as a keypad that responds to touch.
“These clickers need a battery to operate. We created a batteryless clicker by cutting the RFID’s antenna and connecting a push-button switch across the gap. You can use several of these modified RFIDs — one for option A, another for option B, yet another for option C, and so on. When you push the B switch for example, the circuit is completed and the reader records B as your choice.”
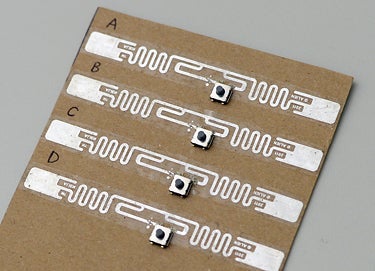
An RFID tag is modified by cutting out a small part its antenna (silver ribbon) and placing a small push-button switch on it. If several modified tags are mounted on a surface, they can act as a wireless keypad.
Light-sensing phototransistors cost 5 to 10 cents apiece, temperature-responsive resistors range from 10 to 50 cents each, and simple push-button switches are just pennies. The cost of hacking an RFID with a sensor or switch is trivial, but its practical implementation has two obstacles to overcome — accuracy and range.
“The light sensor we made by hacking a phototransistor onto an RFID tag is rather coarse-grained,” Abari said, adding that light intensity would need to change by about 75 Lux, roughly the level of lighting in an office, for the luminosity change to be detectable by a reader. Similarly, thermistors, the devices that give a tag the ability to sense temperature, can only detect differences that are at least 20ºC apart.
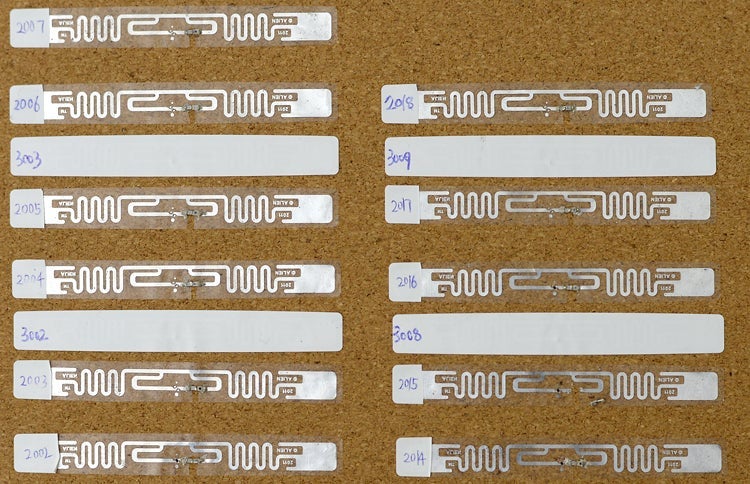
Here, RFID tags are modified by cutting out a small part their antennae and placing a light-sensing phototransistor or temperature-responsive resistor (thermistor) on them.
“To improve resolution, we need to design a reader that has finer granularity for changing transmission power from the RFID tag,” Wang said. “And we need to identify sensors that more precisely change RFID antennas when exposed to changes in the environment. We’re also improving things on the software side — the algorithms we developed — so hacked tags are more accurate and robust.”
A stock RFID tag has a range of 7 to 11 metres, but Abari’s team found that once hacked the tag’s range is cut at least in half to at most 4 metres.
“When you put a sensor on an RFID tag you have to cut a bit of its antenna. It’s now smaller so the antenna doesn’t receive and transmit signals as well as before, which reduces its range.” Wang said. “The sensor itself also reduces the signal to the antenna. If a manufacturer were to design an RFID tag with a sensor from scratch, it would not need to reduce the size of the antenna, so its range would be better.”
“We see this as a good example of a complete software–hardware system for IoT devices,” Abari said. “We hacked simple hardware — we cut RFID tags and placed a sensor on them. Then we designed new algorithms and combined the software and hardware to enable new applications and capabilities. Our main contribution is showing how simple it is to hack an RFID tag to create an IoT device. It’s so easy a novice could do it.”
To learn more about this research, see Ju Wang, Omid Abari and Srinivasan Keshav, Challenge: RFID Hacking for Fun and Profit, MobiCom’18, Proceedings of the 24th Annual International Conference on Mobile Computing and Networking, October 29–November 2, 2018, New Delhi, India, 461– 70.